
Infrastructure Labs
T2 Authentication Failure Investigation
Technician Support

Project Overview
Simulated an authentication failure affecting a standard user account in a controlled environment. Performed a Tier-2 authentication investigation using administrative tools and security logs to identify the root cause and restore user access while assessing potential security impact.Scenario / Context
- User type: Standard (non-admin) local user Operating system: Windows 10 / 11
- Issue observed: User unable to authenticate and log in Impact: Limited to a single user account; system and other users unaffected
- Access method: Investigation and remediation performed via administrative PowerShell
Symptoms
- User unable to log in with known credentials
- Authentication denied during login attempt Account lockout / access restriction enforced
- User reports repeated login failure
Hypotheses / Possible Causes
Now, there are multiple causes for these symptoms, such as an account lockout due to repeated failed login attempts, an administratively disabled user account, an expired or reset password, enforced local security policy restrictions, or a potential security event such as a brute-force attempt.Investigation / Actions Taken
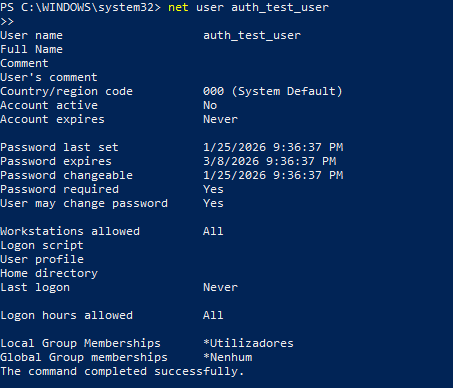
Each possibility was systematically tested:- User account existence and status: Verified the user account configuration and status (Checked using: net user auth_test_user)
- Account disabled or inactive: Confirmed the account was disabled, preventing authentication (Checked using: net user auth_test_user)
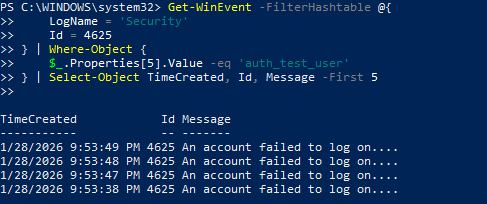
- Account lockout events: Reviewed Windows Security logs for authentication failures and lockout events (Checked using: Get-WinEvent for Event IDs 4625 and 4740) Password validity: Evaluated whether credential issues or password expiration could be contributing (Checked via account properties in PowerShell)
- Security threat assessment: Reviewed log sources and frequency of failures to determine if activity indicated a brute-force attempt (Checked via Security event log metadata)
Evidence
Root Cause
User authentication failure caused by an administratively disabled user account, preventing successful login in accordance with local security policy.Resolution
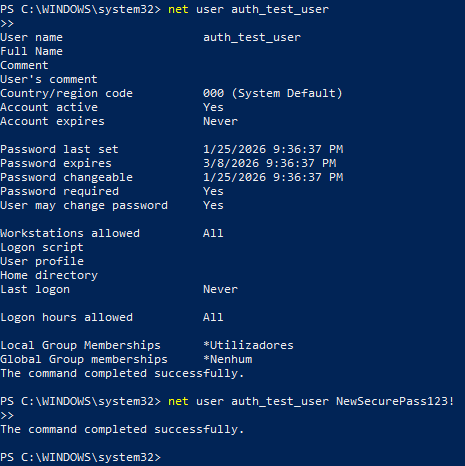
- Re-enabled the affected user account (Command used: net user auth_test_user /active:yes)
- Reset user credentials to restore access (Command used: net user auth_test_user NewSecurePass123!)
- Verified account status and absence of further authentication failures
Preventative Actions
- Document account status changes during administrative actions
- Implement review procedures for account disablement
- Monitor authentication logs for repeated failures Educate users on password handling and lockout policies
- Maintain clear escalation paths for suspected security incidents